The Enterprise Log Integrity Challenge
Log management faces persistent challenges in enterprise environments: ensuring tamper-evidence for compliance, maintaining audit integrity across distributed systems, and establishing provenance for forensic investigations. Traditional centralized logging architectures create single points of failure and vulnerability to sophisticated attacks that can modify or delete critical audit trails.
Blockchain Technology Fundamentals
Understanding blockchain technology is essential for evaluating its log management applications. A blockchain is a decentralized and distributed digital ledger that records transactions in a secure and transparent manner. Each transaction or record in a blockchain is called a block, and once added to the chain, it cannot be altered or deleted. This makes blockchain ideal for applications that require immutable and secure record-keeping.
Potential Benefits for Log Management
The following sections examine the key benefits blockchain could provide to enterprise log management, while acknowledging the significant technical and operational challenges that must be addressed.
NISTIR 8202 provides an overview of blockchain technology.
Blockchain provides immutable records that cannot be altered or deleted once added to the chain. In the context of log management, this means that logs generated by applications, systems, and devices can be securely and transparently stored in a blockchain. This ensures that logs are tamper-proof and can be trusted for compliance, auditing, and legal purposes.
Blockchain provides enhanced security through the use of cryptographic algorithms and consensus mechanisms. Cryptographic algorithms ensure that logs are encrypted and decrypted securely, while consensus mechanisms ensure that logs are validated and verified by a network of nodes before being added to the chain. This makes it difficult for malicious actors to tamper with logs or launch attacks on log management systems.
Blockchain provides transparency by enabling all participants in a network to view and verify logs. This means that logs can be shared securely and transparently among different stakeholders, such as IT teams, auditors, and regulators. This ensures that logs are accessible to all stakeholders and can be used for real-time monitoring, analysis, and troubleshooting.
Private blockchain networks offer improved performance compared to public blockchains by enabling controlled access and optimized consensus mechanisms. However, even private blockchains face significant scalability constraints compared to traditional databases. While distributed processing across nodes can provide some parallelization benefits, blockchain's inherent requirement for consensus and cryptographic verification creates performance bottlenecks that limit throughput for high-volume logging applications.
Blockchain can reduce certain operational costs by eliminating third-party intermediaries and providing built-in audit capabilities. However, organizations must weigh these savings against the substantial computational and storage costs inherent to blockchain technology. The redundant storage across multiple nodes and intensive cryptographic processing typically result in higher infrastructure costs compared to traditional log management solutions. For comprehensive cost optimization strategies across different approaches, see Cloud SIEM cost‑control approaches.
NIST SP 800-92 provides guidance on computer security log management.
Most, if not all compliance and best practices stipulate that securing data and logs are mandatory. Some of these may be familiar but there are many others:
- Homeland Security CDM
- PCI-DSS (Payment Card Industry Data Security Standard)
- HIPAA (Health Insurance Portability and Accountability Act)
- NIAP (National Information Assurance Partnership)
- Common Criteria for Information Technology Security Evaluation
- NIST SP 800-92
- FISMA (Federal Information Security Management Act)
- Sarbanes-Oxley Act of 2002 (SOX)
- Gramm-Leach-Bliley Act (GLBA)
Traditional logging tools can be hacked, tampered with, or corrupted. For example DNC Server hackers in 2016 covered their tracks by modifying logs. For comprehensive security monitoring approaches, see OWASP Top 10 detection strategies.
Current Logging Tools are centralized in a series of identically documented servers/DBs. Logs are often encrypted, but lack provenance and immutability. Therefore, finding and/or modifying the same record in a centralized system is relatively easy.
The Solution
DECENTRALIZATION
Decentralizing data logs on a blockchain eliminates the possibility of a single source being hacked or becoming corrupt. No central source of “truth” means no central point of failure. Once a record is documented on the chain, the centralized failure point is eliminated, and the security of the entire system is increased.
Corruption or hacking attempts to individual records on the chain would appear as outliers to the chain (not matching the majority of the chain) and therefore would be discarded as erroneous.
In centralized systems, a core authority determines the authoritative state and confirmation rights are limited to privileged users or institutions. In decentralized systems, there is no core authority; every participant can access the history of transactions and can confirm new transactions.
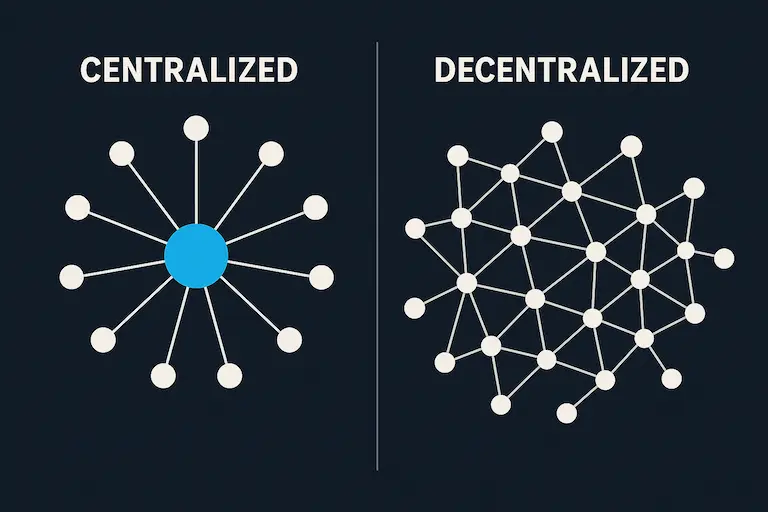 Centralized hub‑and‑spoke vs decentralized mesh‑like connectivity.
Centralized hub‑and‑spoke vs decentralized mesh‑like connectivity.
PROVENANCE & IMMUTABILITY
With Blockchain-stored logs, it is virtually impossible to delete or manipulate the logs because they are immutable and have provenance. As each new block is added, we are creating not just a unique record, but a unique record with a unique history, whereby any attempt to falsify a single record would mean having to falsify the entire chain in the majority of blockchain node instances - not just one entry.
Provenance: Provenance is the chronology of the ownership, custody or
location of a historical object.
Immutability: An immutable object is an object whose state cannot be
modified after it is created.
Any change in a record is documented on the chain, and only after enough (majority) nodes in the chain agree with the change, will that change become “truth”. If the change cannot be verified across the chain(s), then it will become an outlier and not recognized as the truth.
Each block in the chain is informed by the block before it, resulting in a dependent algorithmic relationship & thus attempting to change a block “mid-stream” would result in an incorrect HASH calculation and splitting the chain into a new series of HASHES (more outliers).
What are HASHES/HASHING?
In simple terms, hashing means taking an input string of any length and giving out an output of a fixed length. For example: bitcoin uses SHA-256 which gives an output of a fixed length of 256 bits.
Even a tiny change to a log would result in a new HASH which would be mathematically incompatible with the existing chain, thus creating outlier records.
For Example
| INPUT | HASH |
|---|---|
| This is a test | C7BE1ED902FB8DD4D8997C6452F5D7E509FBCDBE2808B316BCF4EDCE4C07D14E |
| this is a test | 2E99758548972A8E822AD47FA1017FF72F06F3FF6A016851F45C398732BC50C |
Enterprise log management platforms could leverage existing deduplication algorithms to create blockchain-ready hash signatures for critical events. This approach would allow blockchain integration to operate in parallel with high-performance log processing, maintaining operational speed while adding immutable audit capabilities for compliance-critical data streams.
Enterprise blockchain deployment architectures for log management offer diverse configuration options to balance security, performance, and compliance requirements:
- Fully Private On-Premises: Complete control over both log processing and blockchain infrastructure for maximum security
- Hybrid Cloud-Private: On-premises log processing with distributed blockchain nodes across cloud and on-premises environments
- Public Blockchain Anchoring: Private blockchain with periodic hash commitments to public networks like Ethereum for ultimate tamper-evidence
- Multi-Cloud Private: Distributed private blockchain across multiple cloud providers for enhanced resilience
- Cloud-Native: Both log processing and blockchain infrastructure in cloud environments for scalability and cost optimization
These architectural patterns provide flexibility for organizations with varying security, compliance, and operational requirements.
Implementation Challenges and Trade-offs
While blockchain offers compelling benefits for audit integrity, enterprise adoption faces significant technical and economic challenges that must be carefully evaluated:
Performance Limitations: Even private blockchain networks operate orders of magnitude slower than traditional databases. High-volume logging environments generating millions of events per second cannot practically store all data on-chain without severe performance degradation.
Storage and Computational Costs: Blockchain's redundant storage across multiple nodes and cryptographic processing requirements create substantial infrastructure costs compared to conventional log storage solutions.
Integration Complexity: Retrofitting existing enterprise logging infrastructure with blockchain capabilities requires significant architectural changes and operational expertise that many organizations lack.
Selective Application: The most practical approach involves using blockchain for high-value audit trails (privileged access, financial transactions, regulatory compliance events) while maintaining traditional storage for operational logging.
Blockchain technology has the potential to enhance specific aspects of log management by providing immutable records and enhanced security for compliance-critical data streams. However, organizations must carefully balance these benefits against performance, cost, and complexity considerations.
Micro-FAQ
What does immutability mean in logging?
In an append-only model, new records are added while prior records remain unchanged, creating a tamper-evident history that cannot be altered retroactively.
Does blockchain replace traditional log management systems?
No. Blockchain complements existing log management by providing immutable audit trails for compliance-critical data streams while traditional systems handle operational logging.
What are the main challenges for blockchain in log management?
Performance scalability, storage costs, and integration complexity with existing high-volume logging infrastructure remain key implementation challenges.
Next Steps
Organizations exploring blockchain for log management should begin with a comprehensive audit integrity assessment, identifying which log streams require immutable storage for compliance purposes. Start with pilot implementations using private blockchain networks for high-value audit trails, such as privileged access logs, financial transactions, or regulatory compliance data.
Evaluate existing log management infrastructure for blockchain integration points, considering performance impacts and operational complexity. As the technology matures, organizations can expand from proof-of-concept deployments to production-scale implementations that balance immutability benefits with enterprise operational requirements.